My Minecraft server was griefed - learn from my mistakes

A very painful lesson to learn indeed. Not just from a best practice perspective, but also about your own assumptions.
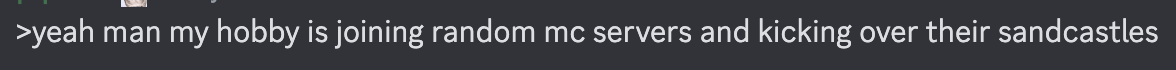
Everything happened today while I was at work. My friends pinged me on Discord to let me know what was happening though I had my notifications on Do Not Disturb, so I didn't know what was happening until it was too late. I saw I had two mentions, didn't realise what was happening, only until I scrolled back on the chat history and started to see more and more messages about unknown player and what was going on. My heart sank as realisation was slowly creeping in until I got to my mentioned messages - two unknown players had logged in and griefed the server. I checked the logs from the past few days and noticed a player called 'matscan' pinging the server, which is how the two griefers probably found the server.
So what happened?
Well, the server was unprotected - it was as simple as that. No Whitelist, no anti-griefing plugins, no automatic backup of the world files. The only thing I did right was to insist on having the server in online mode, even though one of my friends didn't previously own a copy of Minecraft and bugged me to keep the server in offline mode so they didn't have to buy a copy. I insisted, so they bought a copy. Aside from that, that was my failing from a best practice perspective - I didn't take proper provisions to protect my server from griefers.
As for a failing from an assumption perspective, that was my other failing - I assumed I would never griefed. How could I? I never posted my server's IP anywhere, nor did my friends. How could anyone find it? I didn't think they could due to obscurity, so I assumed we would be safe. Who would care about one tens of thousands of Minecraft servers, let alone find it?
The Backstory
I first got into Minecraft server hosting when I was 12-13, right on the release of Minecraft 1.1 (that's not a typo - 1.1, not 1.11). I finally got my own copy of Minecraft and wanted to play with my friends, but none of my friends knew how to set up a server let alone port forward or understand basic networking, so I took it upon myself to learn everything I needed to set up a server my friends could join without Hamachi or Tunngle; to be able to connect to a server by just giving an IP address and nothing else, like a true pro. At least, I thought I was. It's thanks to this simple decision that led me to learn about the rabbit hole that is tech, self-hosting, servers, etc. but that's a story for another time.
By being the one who learned to host a server, I understood the difference between a Vanilla server and a CraftBukkit server, what it means to go around griefing servers, protecting yourself, knowing about anti-griefing plugins like Big Brother, having permissions set up using PermissionsEx, and a whole host of other things you could do. However, I never needed to do it because I only ever hosted for my friends and didn't post my IP anywhere; I never intended to go public and try to build a community. And for a very long time, that's all I ever needed.
The Modern Age
However, in this day and age of public Minecraft servers, it turns out griefing is still alive and well, and it's an even bigger beast than I knew it: more sophisticated cheat clients, server scanners, session authentication spoofing. Watching iCanHasGrief on Youtube back in 2012 led me to think these guys were unique in what they did, and that generally, people didn't hunt servers and try to grief them, let alone be able to do it like they did. Back in the day, there was also no such thing as a server scanner. Or at least, not one as easily available.
My biggest mistake was not having a whitelist. That, in itself, would've probably prevented the grief by preventing unauthorised players from connecting. And it would've made sense, as our community is very small— there are 7 or so players, including me—so it wouldn't be too much bother for anyone at all. But I thought to myself, "I don't need to whitelist. How is anyone ever going to find our server? It'll never happen to us". But it turns out people regularly scan any publicly accessible servers, particularly those hosted on port 25565, Minecraft's default server port. This is a really common abuse method, sniffing out unsecured servers on default ports and attempting to log in to them. It's for this reason that if you ever host a public-facing server or even your home server accessible via SSH to the wider internet, either change the default port and/or put in proper measures in place so you can stop mass automated attacks dead in their tracks at the first hurdle.
The Lessons Learned
If you're like me and own your own (game) server or some other public-facing service on the internet, learn from my mistakes and put proper measures in place. And it doesn't even have to be a Minecraft server. These are the steps I'll be taking to recover from the grief, though you can apply this to your own hosted service:
- Use a whitelist (if it makes sense to do)
If you host a large server or if you play the sort of game where griefing annoys people at most and doesn't have the ability to do permanent damage, then you may not need to whitelist. But if you play a game where things can be broken or destroyed or if you don't want to be annoyed by randomers, absolutely set a whitelist in place - there's no excuse not to do it. - Set up anti-griefing or anti-abuse measures in place
If you run a Minecraft server, a plugin like CoreProtect or other solutions are essential to tackle griefing. Whether it's being able to undo the grief or prevent players from griefing in the first place, a good protection is invaluable.
Equally, you can apply the same principle to something like having a home server that you've exposed to the internet and can access remotely via SSH. This is arguably more detrimental if it goes wrong than your Minecraft world being destroyed which is why people often suggest not to expose SSH to the internet and instead connect via VPN, though you can set up public-private key authentication only and disable password logins, disable root login, install Fail2Ban on your home server, and/or change your SSH port to something other than 22 to help protect yourself. - Backups, backups, backups
Even if you secure yourself from griefers or other damage, backups are invaluable for any scenario. Somebody set fire to an entire forest? You accidentally deleted your server files? The power goes out and your files are corrupt? A good backup practice will help mitigate these disasters. - Never assume anything, particularly when something is at stake
My biggest downfall was assuming we would never get griefed, even if our server was publicly accessible because I thought we would be secured by obscurity; I didn't think people would even be able to find our server amongst tens of thousands, let alone care enough to connect. It's because of this assumption and a false sense of security that I didn't bother to take the proper precautions, even though I knew about them and their importance.
My heart aches as I reflect on the grief while writing this post, though that's primarily because I feel responsible for what happened to my friends. We were all griefed, but I'm the admin of the server - it was and it still is my responsibility to make sure the server runs well and is protected. Their builds were griefed on my watch because I didn't take the proper precautions.
With all of that said, there is a silver lining to this unfortunate situation. Although buildings were griefed, the damage could've been much worse. We were griefed at a point in the server when we started only a week ago and hadn't built that much yet, so we stood to lose far less than if we were weeks or months into the server.